We have a pretty big problem with our technology power consumption. On average, a server uses between 400 Wh and 900 Wh. By official sources, different vendors sold almost 100 million units for the period between 2010 and 2020. And ten years is the average lifecycle for a server. So, at the moment, we can calculate that to have running just the server part of the Internet, we must generate 50 GWh. And most of this power is coming from traditional power sources, which can be a target of a cyber attack, as we saw from the Colonial Pipe case.
According to another official source, the Internet has around 5 billion daily active users. On average, every user will have at least one personal computer and a smartphone. For every four people, we have one network router. For every twenty users, we will have a network switch provided by their service provider.
An average consumption per hour for a personal computer is around 200 Wh, for a smartphone is 1 Wh, for network switch and routers are 10 Wh. Now, this makes an additional 1000 GWh + 5 GWh + 100 GWh. Servers, network equipment, and smartphones work 24 hours, and users usually browse around for 6 hours on average, making a total of 9720 GWd or 405 GWh.
So the average consumption of the Internet is around 405 GWh. Just for comparison – one nuclear power plant can produce 1 GWh. So we need the equivalent of 405 nuclear power plants to keep everyone online.
There are two leading solar solutions for commercial use at the moment. The first option is the standard solar panel. The average production of such solar panels is 320 Wh. To cover the needs of the Internet using only solar panels, we shall need 1.3 billion of these solar panels placed around the World. The second option is solar power towers. The main idea of solar power towers is to establish many digitally controlled mirrors, reflecting its rays into a tower full of salt depending on the Sun location. When the salt is molted, it is combined with water, evaporating to a turbine. The most significant such installation is Ivanpah Solar Power Facility, with a production capacity of 392 MWh. To cover the needs of the Internet, we shall need around 1,000 such structures.
However, to build a solar-based solution, we must consider the following problem: there are only around 12 hours of daylight in most locations. There are two mitigations of this problem – the first is to double the number of installations and make sure they cover the 24 hours interval for everyone by strategical placement. The second is to double the number of structures and install batteries to preserve the generated energy for night use.
Our first mitigation creates an interesting geopolitical situation with a large number of dependencies. For the second mitigation, let’s calculate how many batteries we need to preserve the energy for night use. 405 GWh multiplied by 12 hours make around 5000 GWn. A standard Tesla Powerwall unit can store 13.5 kWh. We shall need approximately 370 million units to preserve the energy during the night.
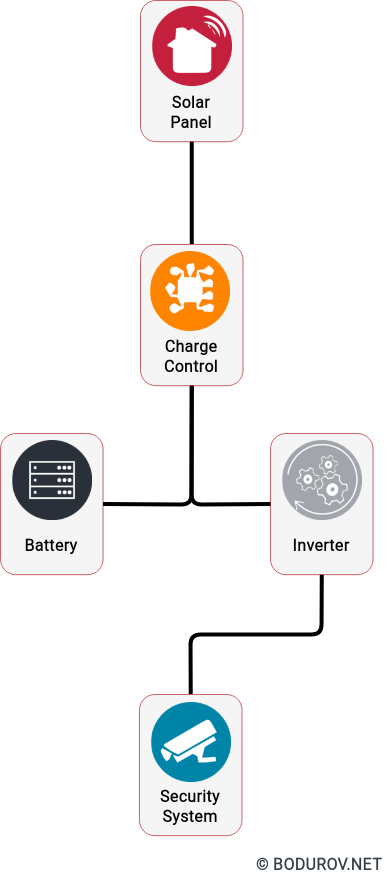
In conclusion, solar power can be an exciting alternative to traditional power sources. In terms of cybersecurity, it could make your network and even alarm system not so dependent on power coming from the grid. The standard way of having a backup is to have a petrol-based generator unit. However, you must fill a generator with petrol, which means that the system is not 100% independent. It is essential to know that the solar power alternative can give an extended backup period, but it will come with a higher price, more complex setup, more expensive support, etc. However, it can offer quite a good way of making your security more robust.
Legend:
Wh – Watts per hour
kWh – Kilowatts per hour = 1000 Wh
mWh – Megawatts per hour = 1000000 Wh
GWh – Gigawattas per hour = 1000000000 Wh
GWd – Gigawattas per day
GWn – Gigawattas per night