Please check the previous part – here.
After we already discussed how to assure your physical security and your network perimeter. The topic for the following two parts is the security of your hardware devices. And especially, I shall give you some ideas on how to secure your personal computer and your mobile phone. I shall provide a sample budget for a security-oriented personal computer, laptop, and mobile phone at the end of the parts. In the budget, I shall put the software appliances as well.
But before doing this, let’s have a short discussion of what a computer is and how we use it. The formal definition of a computer is:
A computer is a machine that can be programmed to carry out sequences of arithmetic or logical operations automatically. Modern computers can perform generic sets of operations known as programs. These programs enable computers to perform a wide range of tasks.
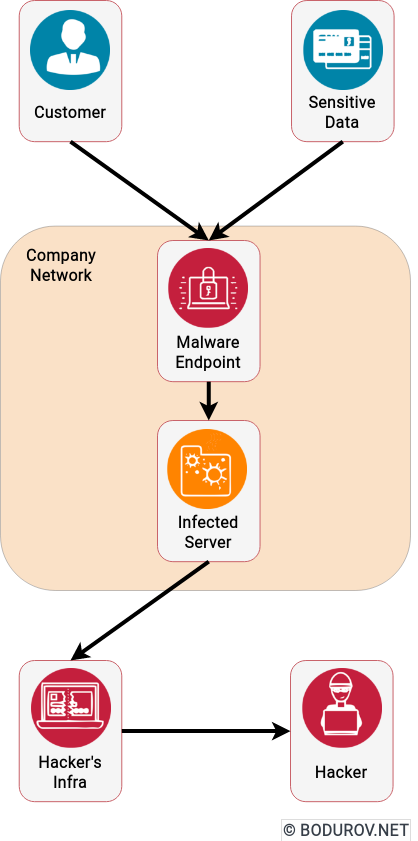
In other words, we have a machine, which works with data and can perform operations on it. It is similar to what our brains do for us but in a different way. In terms of computer security, it is essential to understand that your computer is a data carrier and data generator. The goal of your security awareness model is to protect the data and the generator logic. So we have to treat our computers the same way we treat our brains when we don’t want to share data. Aka by making sure we took all the necessary steps to secure access to our information.
So let’s do it. We start with:
Personal Computer/Laptop
We shall discuss the security of laptop computer because it has a more significant amount of attack vectors. We can apply the same list of attacks to workstations.
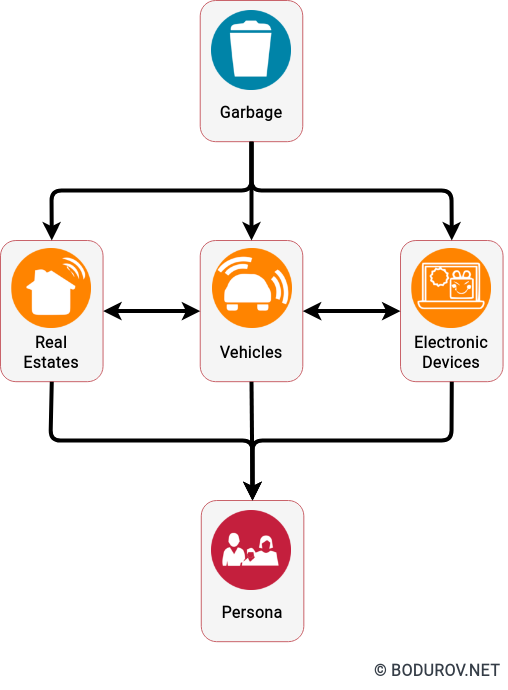
By definition – A laptop, laptop computer, or notebook computer is a small, portable personal computer (PC) with a screen and alphanumeric keyboard. It is important to note that a laptop is a total nightmare for your computer security policy in the physical security realm. It inherits the traits of all the hardware devices, including the ones related to garbage. Securing laptops is almost impossible, and a dedicated attacker most probably will manage to penetrate the defenses of your laptop one way or another. But let’s list the different attack vectors your laptop has.
- Theft: By being mobile, any laptop is a mobile data carrier similar to your paper documents and USB flash sticks. And by that, a dedicated attacker can steal the computer and gain access to your data. It is essential to mention that any encryption mechanism can slow down your attacker, but you can not determine whether it will stop him.
- Location-based attacks: Companies such as Hak5 promote an exciting set of tools used for location-based attacks. They can penetrate your WiFi network, and even there are devices named RubberDucky. They look like a standard USB flash, but essentially they are cheating your computer that they are keyboard devices and execute a penetration script.
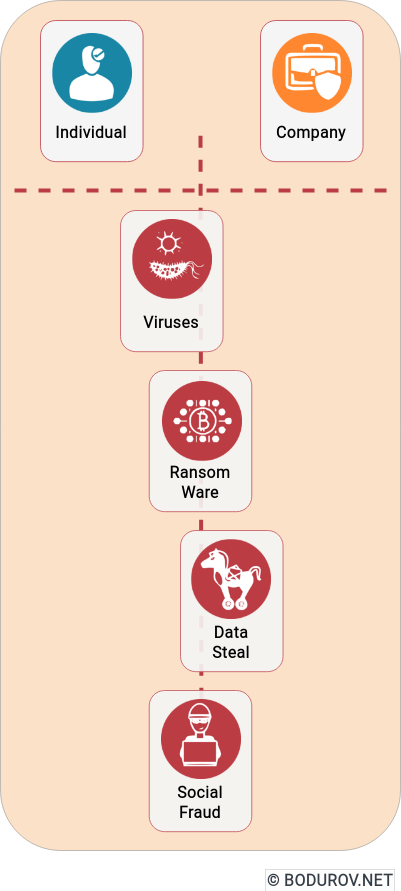
- Malware: There are many types of malware, but these are most dangerous in terms of cybersecurity: trojan horses and ransomware. Both of them steal your data. In case of ransomware, you have to pay, and at least you receive notification that something wrong happened. In the case of trojan horses, you have no idea what is going on with your data.
- Misconfiguration: Most of the laptops do not come with proper security configuration by default. Users without formal training can not configure the system, and it remains unsafe until a hacker penetrates it.
- Pirated Software: Torrent trackers are a terrible place to download software. Usually, the cracked versions of the popular software come with already preinstalled malware. It is highly advisable to use open source or paid products.
Listed threats are only part of a long list of attack vectors an organization must take care of. Still, they are a good starting point, and if your small team manages to stop them, it can reach a good cybersecurity level.
Smartphones
After the introduction of IBM Simon, the smartphone industry had rapid growth. These days, devices are as powerful as a ten-year-old computer and can perform various tasks, which people kept only for computers for a long time. It is fantastic, but they are even worse in terms of cybersecurity than your laptop. They inherit all of your laptop’s problems with even smaller size and limited control over the hardware. They are a nightmare in terms of computer security. But let me list the different attack vectors which your smartphone can introduce:
- Outdated Operating System: To further push technical progress, hardware vendors usually discount older than four years old devices. And by discount, it means that these devices do not receive security patches and the latest version of their operating system. This approach leaves thousand of people without proper cybersecurity defenses.
- Laptop Attack Vectors: As a less powerful computer, every smartphone inherits a laptop’s security problems. Even worse, once you store your data in your smartphone’s internal memory, it is almost impossible to erase it securely.
- Conversation Sniffing: Hackers can use your smartphone to sniff your daily conversations by being constantly held near to you. Many hardware vendors implement security measures versus this kind of attack, but people must still be aware that such an attack is possible.
Next part is here