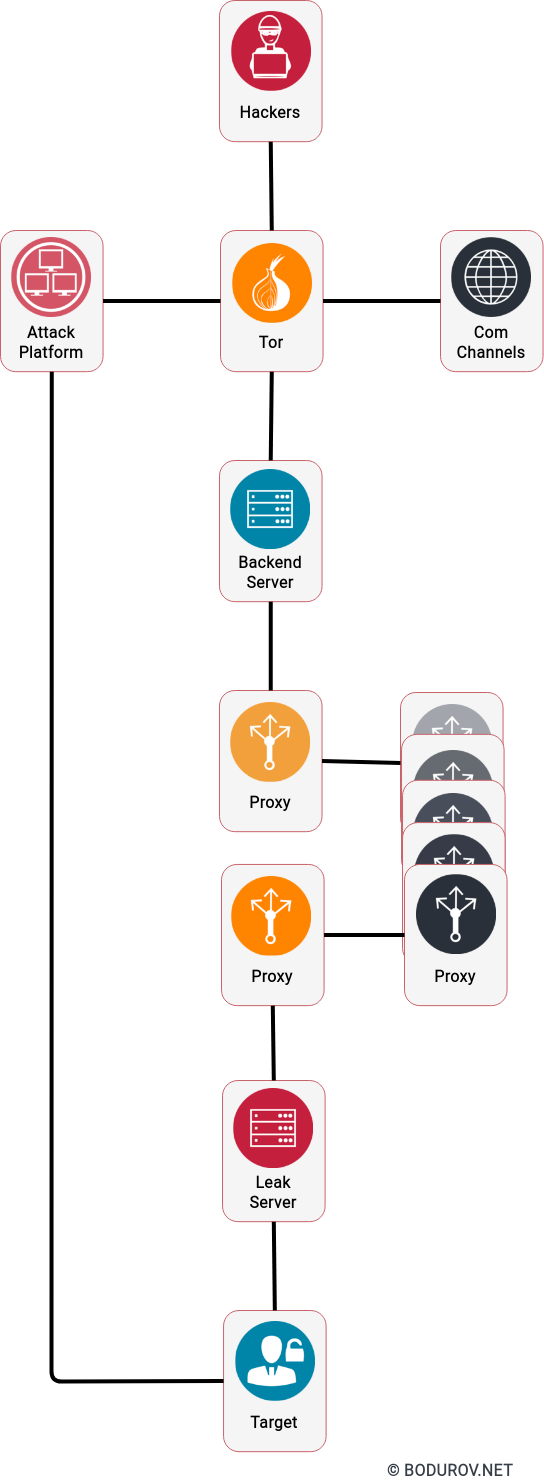
Cyberwarfare is our new reality. There are many examples where state and non-state actors were involved in hacking government-based organizations. Reasons for these attacks are different, but essentially financial gains and personal vendetta are the two most common. However, we could add one more reason for a cyber attack – an attempt to take leverage. Sometimes these cyber-attacks can sabotage even natural resources. Let us see if we could find any example for it or not.
The GERD case:
One example of cyber warfare for natural resources is the one related to the Grand Ethiopian Renaissance Dam. The dam is a reason for a dispute for a long time. However, at the end of June, a hacker group executed many attacks on the Ethiopian government’s websites. The attacks targeted information technology infrastructure, communications, and websites of public service agencies, security organizations, and other public and private institutions. On June 18, the hacker group announced that they would strike six other websites in response to the Ethiopian government intransigence on the GERD issue. As with every cyberattack origin of the attack is unknown.
The Colonial Pipeline case:
Another exciting and relatively soon case is the one with the Colonial pipeline. Ransomware managed to block the entire infrastructure of the company. In response, Colonial Pipeline Company halted all of the pipeline’s operations to contain the attack. Colonial Pipeline paid the requested ransom (75 bitcoins or $4.4 million) within several hours after the attack. The hackers then sent Colonial Pipeline a software application to restore their network, but it operated very slowly. How the attackers reacted is a little bit suspicious because usually, attackers want you to receive your data immediately after you pay. In another case, no one will ever pay them again. And most of the cybercriminals are after the money. The origin of this attack is unknown.
Florida water systems hack:
A plant operator for the city of about 15,000 on Florida’s west coast saw his cursor being moved around on his computer screen, opening various software functions that control the water being treated. The intruder boosted the level of sodium hydroxide—or lye—in the water supply to 100 times higher than normal.
Sodium hydroxide, the main ingredient in liquid drain cleaners, controls water acidity and removes metals from drinking water in treatment plants. Lye poisoning can cause burns, vomiting, severe pain, and bleeding. After the hacker exited the computer, the operator immediately reduced the sodium hydroxide back to its normal level and then notified his supervisor,
In conclusion, governments must treat their systems similar to what big corporates and organizations do. Critical infrastructure needs proper defenses, and a good security level is not achievable without appropriate resources and budget. With the coming of the Internet, the World is no longer a disconnected place with multiple local communities. Now we live in an era where everyone connects to everyone else up to a couple of milliseconds. And as we can see the cyberspace more and more can affect our real lives.