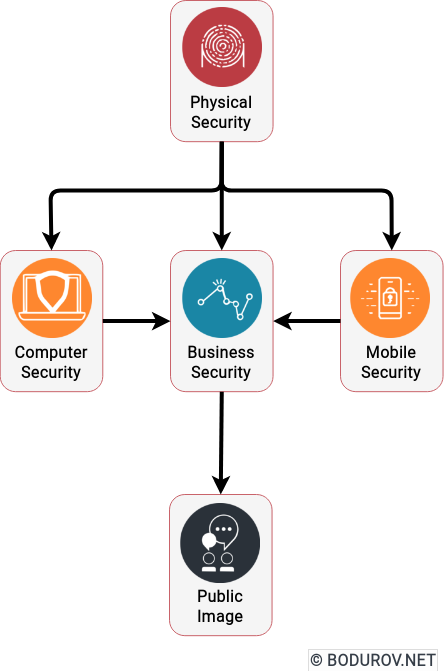
In the next couple of months, I shall write series of articles covering the topic of cybersecurity on a limited budget. The idea is to show you different methodologies for how to keep you safe without spending too much. The articles will cover various topics such as physical, computer, and mobile security. Additionally, as part of this series, I shall publish two articles covering business security and public image preservation. A final overview article will summarize all written and consist of a sample budget to cover your cybersecurity needs. It will be a good reference for startup and SME organizations. They can use it to establish or upgrade their cybersecurity defenses.
Different authors wrote many books and articles on keeping your computer and mobile phone safe for the past couple of years. Unfortunately, most of these writings ignored one fundament of cybersecurity. Without properly secured hardware devices, all of your defenses are meaningless. Of course, other authors wrote whole books on physical security, but no one covered it from a cybersecurity perspective. This article aims to cover this perspective and give an exemplary workflow of achieving adequate protection on a tight budget.
So let’s start it.
There are multiple online threats to your security, and let’s start with them. During my time working in different companies, I saw many people neglecting these threats. Fortunately, these mistakes did not lead to escalation. But let me list them and give a short explanation of how they can affect you.
- Social Platforms: Sharing your life is an excellent way to keep in touch with your friends and relatives. At the same time, it opens possibilities for hackers to monitor you. Monitoring is essential for other types of attacks. Usually, hackers execute these attacks in the following phases.
- Shared Travel: Shared travel is a new way of traveling around. It increases comfort and lowers down the price of travel. At the same time, travelers organize the travel in public social media groups. Everyone can join this group and monitor when you travel. Such information is valuable, mainly if attackers target your home or office space.
- Cyberstalking: Your online persona can trigger destructive emotions, and usually, this evolves into cyberstalking. It is essential to limit down exposure to such threats because they can end up into physical ones.
- Navigation Devices: Using online navigation is lovely in terms of comfort, but most navigation software collects a considerable amount of data. Hackers can correlate this data to your real persona and monitor your life and travel plans.
As you can see from the list, different parties can monitor a good number of your online activities. With enough time and resources, these parties can execute future attacks on you. For real estates, we can create a similar list:
- Social platforms: The situation is the same as in the previous paragraph. Attackers can execute multiple attacks using the information gathered by your social media accounts.
- Smart Home Assistants: Smart assistants are hardware devices placed in your home. Usually, they have always turned on microphones to catch your commands and execute different orders regarding your house. At the same time, they can be hacked and used to monitor your activities.
- Camera arrays and sensors: These days, many people install cameras and sensors attached to the Internet. Without proper cybersecurity protection, attackers can use these hardware devices to monitor your activities.
- Laptop and smartphones: Same is true for laptops and smartphones without a proper security defense. Hackers can use them for monitoring your activities.
Intruders can use all of the upper threats to execute next-stage attacks on your real estate. Another aspect of your physical security is the security of your vehicle (car, truck, and other vehicles). As vehicles become more and more intelligent and automated, their vulnerability to hacks increases. Next are the common threats you can face with intelligent vehicles:
- WiFi Access Points: Modern cars have WiFi access points in them. Or in simple words, this is a network router, which is part of your car’s computer. This router can be hacked and used for malicious activities.
- Smart Locks: The current trend in the automotive industry is making cars more and more intelligent, including their locks. Of course, this is a wrong decision in cybersecurity because the makers increase the penetration surface with new functions and capabilities. Some of these locks use older encryption protocols, not updated with years.
- Autopilot: Most modern e-cars support autopilot as a feature. Autopilot is a fancy name for a sophisticated computer program, which drives the car for you. And being a program, autopilot runs on a computer, and this computer can be hacked and used for malicious activities.
- Real-time Updates: Newer car models receive constant updates on the fly. They follow the process your operating system uses to update itself. How secure this process is rarely publicly disclosed.
Next part is – here.