User identity and security have continuously been reinforced in the organization by the use of strong passwords. User accounts tend to be restricted based on specific passwords typed. However, that has changed due to the technology rise that has wiped away the traditional password methods. Although some organizations still prefer passwords, authentication is slowly evolving to be passwordless due to convenience and efficiency purposes. Identity-based passwordless authentication is the focus of organizations and IT migration.
Passwordless authentication helps curb the insecurity that is common with organizations. The trends in cybercrime require that organizations implement robust measures of security in helping minimize the consequences.
Most technology-driven organizations have already implemented identity-based passwordless authentication. One popular method is biometric authentication as the main component of identity-based passwordless authentication. It integrates the biological features to develop some of the most effective solutions for signing into information systems and corporate portals. Significantly, a better approach to the management of user profile security and accessibility is by leveraging the biometric features and integration with IT to help promote a seamless process of identification. However, it is essential to ensure that the biometric data stays on your device and is adequately encrypted. In another case, once stolen, anyone can reuse it. Other methods use directly public and private key cryptography to achieve the same results.
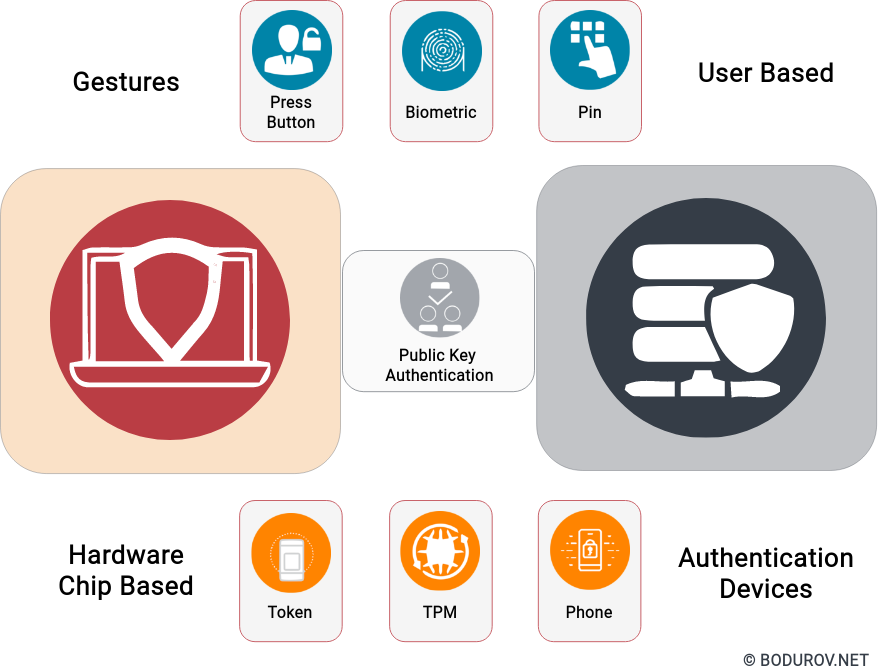
The uniqueness and strength of restricted access are robust in passwordless protection. Its features help in the promotion of quality and proper protection techniques, which are vital. Considering diverse approaches and key organizational security management measures, organizations have opted for identity-based passwordless authentication.
Cybersecurity is a significant concern, with hackers targeting high-profile organizations and creating weak points while accessing sensitive information. According to recent research, technological migration has been towards passwordless identification. The users do not have to use password authentication to access the organizational profiles. Necessarily, integration and passwordless leverage are vital in implementing the proper security protocols to achieve the desired security goals.
The feasibility of identity-based passwordless authentication is another competitive advantage. Passwords are tedious. Every time you enter them, you waste time as a significant impediment to a flawless work process. Most employers prefer passwordless authentication because they implement strategic and focused measures to improve access levels and ensure necessary and fundamental elements.
Passwords are the primary targets for hackers since they only have to master the keywords and process execution, which results in cracking of the security architecture. Biometric technology is the best way to focus and help advance its security needs, mainly by implementing efficient identification processes.
According to attackers’ behavior analytics, a strategy to reduce the attacks is by sensitizing people to implement passwordless authentication. Natural features are unique, and the level of security provided by investing in such technology is excellent. Howerer, the future will show whether it will help to improve safety and to meet various businesses’ needs regarding cybersecurity solutions.