Several months ago, I had to make a trip over the weekend to a city sitting 160km far from Burgas. I decided to take the more direct route, which goes through Stara Planina, one of the mountains located in Bulgaria. There were many trucks on the road. Other car drivers and I were driving behind them without a clear opportunity to overtake. I wanted to check something on my smartphone, and I misclicked on the WIFi network indicator. To my surprise, the list showed one item – a WiFi network with a mobile phone number as its name.
And then it clicked in my mind that the two cars in front of me, trying to overtake the truck for the last twenty minutes, were most probably a company traveling together, and the owner of one of the cars was sharing his/her hot spot with the passengers. He/She had most likely decided to name his/her WiFi network with his/her mobile phone number.
The defensive cybersecurity expert in me started clicking with his tongue in disapproval because I now had the driver’s phone number and his/her car registration plate. Additionally, I had the knowledge that someone in the cars in front of me was using the listed WiFi network. With all that information, a motivated attacker could do the following exciting things:
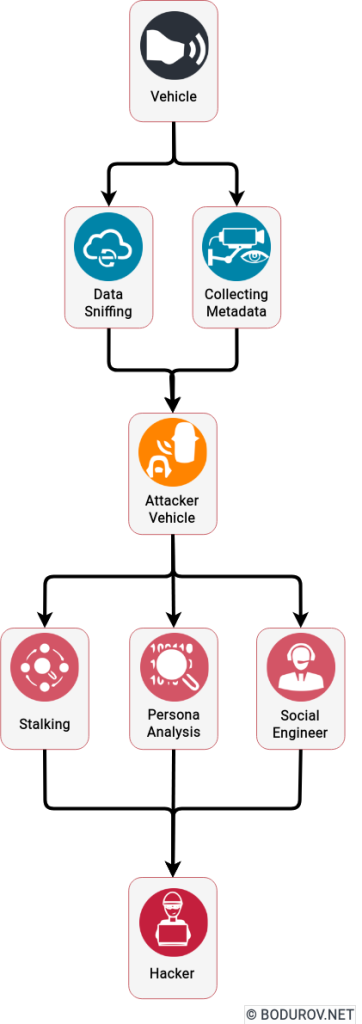
- Find the driver of the car: With some search in the dark web, a motivated attacker could find illegal databases with phone numbers and vehicle registration plates mapped to their owners. Additionally, if the phone number owner had posted an online ad for something using that number, it usually got indexed by most search engines.
- Get the metadata of the WiFi users: The WiFi search protocol is quite leaky in terms of metadata sharing. For example, your WiFi client usually broadcasts all the network SSIDs your device was connected to for the last couple of days. Using this weakness, we could collect that data for every device connected to the hot spot and use that data for malicious activities. One such activity is finding the places where the owner of any of the connected devices was. Especially if the owner of the devices regularly connects to public WiFi networks in hotels, cafes, etc. There are many databases in the dark and on the regular web with such mappings betweens WiFi SSIDs and GPS coordinates.
- Enforce the WiFi client to connect to a malicious endpoint: With the proper equipment, the attacker could enforce all the WiFi clients to connect to his/her malicious WiFi endpoint and sniff all the data coming from the devices. Modern smartphones software usually comes with proper protection, but bugs happen, and the attacker could keep the collected data and decrypt it offline or in the future.
- Social engineer the owner of the car: A motivated attacker could call the owner of the vehicle and present himself/herself as a police officer asking the owner where the car is at the moment and that someone made a complaint about the vehicle parked not correctly. To make the lie ever more truthful, the attacker could tell the driver that he/she and his/her colleague must go and check the car personally. If this attack is performed after work hours, the victim will probably give his/her an address near his/her home.
In conclusion, the car driver in front of me had a bit of good luck that I was driving behind them, but not a criminal. In another case, all of these attack vectors could happen. Unfortunately or fortunately, cars have become more and more intelligent. But with becoming more intelligent, more and more security holes have become open for attack. We should be concerned, especially with the increasing adoption of electric vehicles in our lives. They are, in fact, computers on wheels. And these computers have and will have more and more security vulnerabilities.