In last week’s article, I spent some time discussing the disadvantages of penetration testing. The main limiting factor for every red team is the client’s engagement policy. Usually, it is not comparable to a real-life attack. However, at the same time, some of the latest developments in the field are pretty disturbing and could be used by hackers for malicious activities.
One such gadget manufactured by Hak5 looks like an ordinary USB charging/data cable, but it comes equipped with the latest keylogging capabilities. Additionally, the cable supports the following features – Keystroke Injection with DuckyScript™, Keylogging (650,000 key storage), USB-C Smartphone & Tablet Keystroke Injection, Remote Access by WiFi, Customizable Self-Destruct, Multiple storage slots for large payloads, On-Boot payloads, Remote Trigger by WiFi (Geofencing), Long Range WiFi Trigger (2 KM+), Control from any Web Browser and Scriptable WebSocket. In short, that cable is a fully working micro-computer with remote access capabilities for loading payloads and executing them without the victim’s knowledge. As a bonus, it looks exactly like the standard USB to USB-C cable. They either offer versions for Macs.
A creative attacker can think of many uses of these cables. For example, they could ask you to lend them your cable and switch it with the malicious one. They can break into your home/office and swap the cables. They can load the whole supply of a computer shop with these cables and sell you one. The options are almost limitless. With that gadget, you virtually can not trust any cable or flash drive you buy from your hardware equipment supplier, neither your friends nor your family’s equipment.
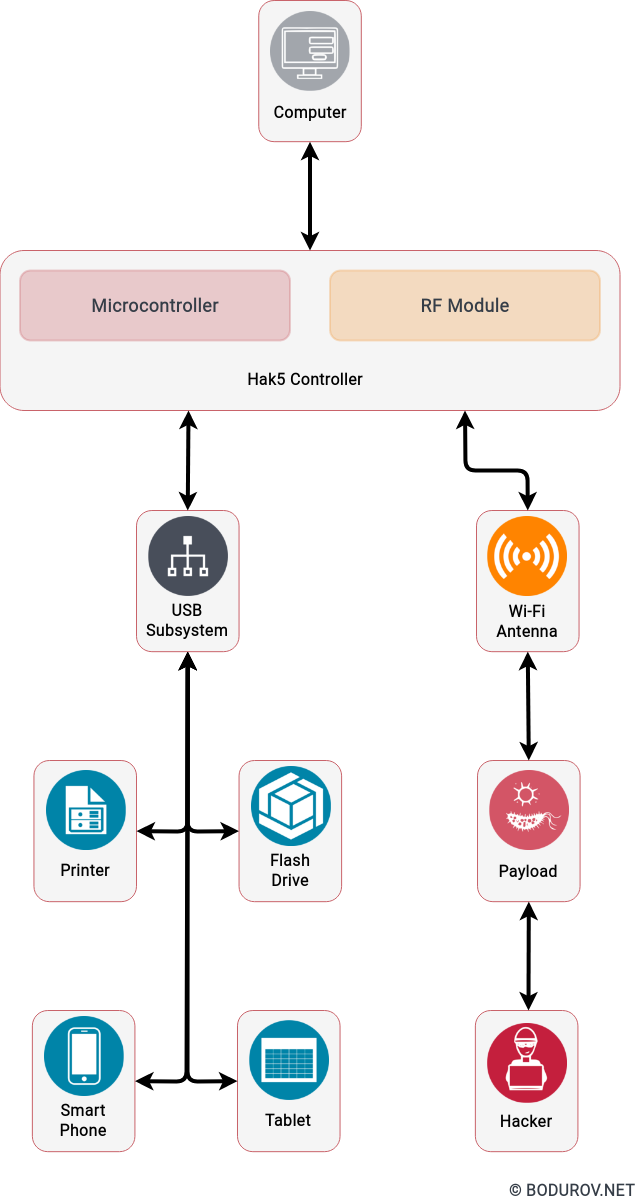
We could imagine that the next step for companies such as Hak5 is to embed a fully blown ADB build into the cable and enable remote penetration attacks versus smartphone devices. Such cable will be quite an exciting gadget and could encourage even more attack scenarios.
I have wondered why such equipment is not treated the same way as weapons for a long time. The relative easiness of manufacture and use of such gadgets make them more and more dangerous. Without regulations or even government-based permissions, more and more people will have access to them. What is the guarantee that they will not end in the hands of black hat hackers or criminals? Not to mention that every white or gray hat hacker could potentially go rogue and become a black one. What is the guarantee that such gadgets will not be used for malicious purposes even by licensed professionals?
In conclusion, penetration testing’s land space has become more and more concerning. Without a good set of regulations, we could soon see many people using military-grade hacking gadgets, turning the defensive part of cybersecurity into a terrible nightmare. In any case, many defenders will not be fascinated by the idea of wrapping their USB cables and flash drives with aluminum tape[1] every time they buy new hardware. Sure, it is a cheap way of blocking radio waves, but the aesthetics will not be on a high level.