Red team exercises and penetration testing became our new reality. Especially with COVID-19 and the additional boost to digital transformation, we are more and more digitally dependant. Many countries have started legally enforcing business and governmental organizations to ensure better their cyber security defenses. And the best way to do that is to have regular penetration testing drills once or twice per year.
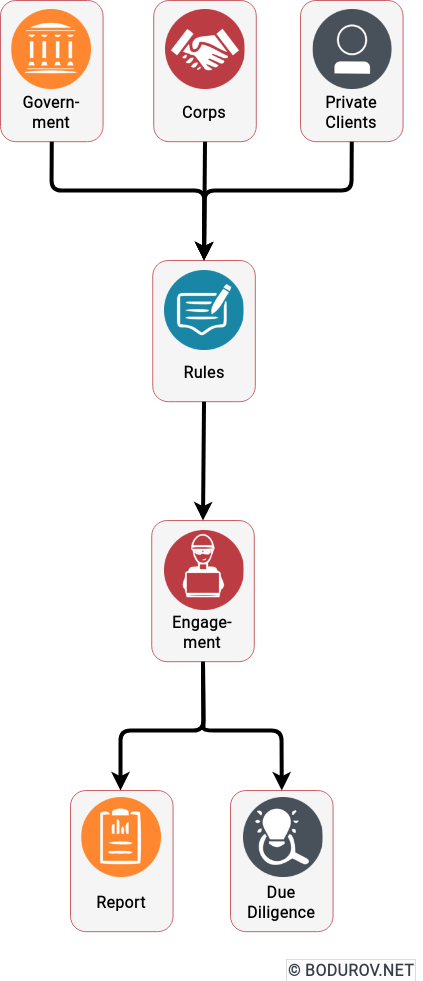
However, we should ask ourselves how effective is this practice and whether it provides a good level of security for our data and assets. To do that, let’s analyze what the usual workflow of doing a penetration test is. Every engagement in cybersecurity starts with a legal contract, which defines the rules of engagement. In this legal contract, the defending side, the client, negotiates the regulations with the attacking side, aka the penetration testing company. In the case of 3rd party requirements such as governmental and corporation integrations, the rules are defined by the 3rd party. They can even give you a list of “trusted” penetration testing companies from which you have to choose. For example, when we had to do a security audit for Google and Microsoft to allow our integrations, they provided the list of auditing partners we had to use.
And here is one of the main problems with penetration testing – there are rules of engagement. In the Real Word scenario, there is no such thing as a set of rules. The dedicated attacker can do whatever is necessary to penetrate your defenses, and he/she will not abide by the law. Comparison to conventional military drills is not practical but could even be harmful to your team’s attitude. It is much better to compare the attacker modus operandi to what guerilla fighters do, such as asymmetric warfare, without rules, requirements, etc. Attackers will do what is necessary to penetrate you no more or less.
The second problem with penetration tests is that the attacking team usually has limited time to penetrate your organization. The whole economy around red teaming is based on projects between two weeks and two months long. After that, the attacking team must go to the next assignment. In comparison, real-world hacker teams are usually part of criminal syndicates, and these criminal syndicates have other sources of income such as human trafficking, prostitution, drugs, and weapons. They can happily try to hack one organization for a year or more, especially if it is a big enough target.
And last, but not least – different motivation. In the red team case, the motivation is to abide by a requirement or by law. It means that the penetration team will ensure that the system passes the requirements and rarely will do more. When we speak about real hacker groups, usually we have a pretty limited set of motivation types – money and personal vendetta. Both of these are much higher on the motivation scale than a simple requirement fulfillment.
In conclusion, penetration testing is a helpful activity; however, it is not a panacea. The results coming from it gives a piece of information for your organization’s current cybersecurity state. Unfortunately, the limited scope of every penetration test will not give you a 100% guarantee that attackers can not destroy your defenses. It is much better to treat the red teaming as part of our cybersecurity strategy and valuable security tools.