Please check the previous part – here.
The same concerns as to real estate apply to all vehicle-related threats. Hackers can use your vehicle to track your activities and to decide when to execute an attack towards you. As a final list of perils, I would like to mention the dangers related to garbage. Most people do not consider their garbage as a cybersecurity threat. However, the truth is – this is usually the best source of intel for a given hacker organization. Let me list the different threats your garbage generates, and after that, we can create a simple budget of how to keep your and your devices secure:
- Paper: Every paper document with personal data, addresses, or buying preferences leads to information leaks, which any hacker group can use to penetrate your defenses. A paper retention policy is a must for every organization these days.
- Hard Drives: Techniques for data forensics become more and more advanced. Hackers can use these techniques to retrieve data from hard drives and SSD drives found in the garbage. It is better to treat your Hard and SSD drives as paper documents and not resell or throw them away.
- Mobile Phones: Modern mobile phones are computers. Deleting data from them is pretty tricky. To keep your organization safe, you must treat them similarly to paper documents and hard drives.
- Electronic Devices: Every smart device in your home and office is a low-level mini-computer that stores and records data. Hackers can read the storage chips of these devices with proper machinery. They can use the data stored there for malicious activities.
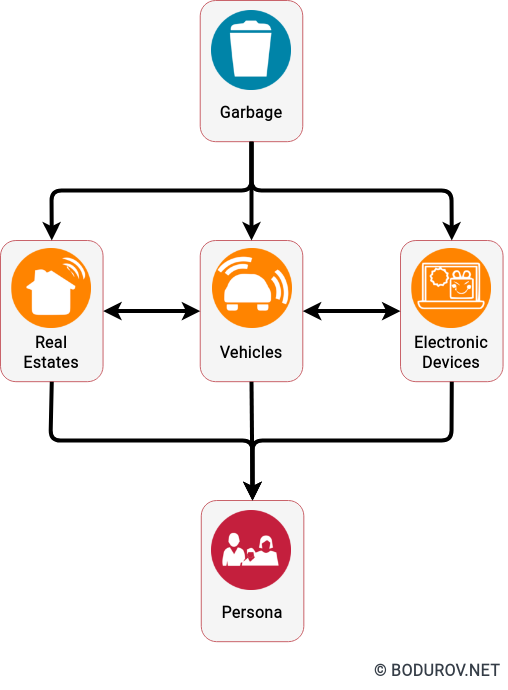
You can notice that the number of attack vectors to your persona is quite significant. And we are only in the physical security realm, without mentioning any digital space. As promised at the beginning of the article, I shall present a simple list of tools and activities, together with a budget. Using them, you can set up your cyber defenses on a limited budget:
- Hardware toolkit (100$): This toolkit will give you the availability to disassemble all of your electronic devices and destroy them. If you have better knowledge of electronics, you can cut the power of your laptop microphone and camera.
- Paper Shredder (50$): A shredding machine can destroy paper documents, credit cards, and everything which looks like a paper-sized card. Still, cutting through the papers is just a first step, but not enough.
- Camping Gear (50$): There is no better way of document destruction than burning them. With camping gear, you can go to the woods, have a barbecue, and meanwhile destroy all of your not-needed documents.
- Safe (500$): Paper is the ultimate data storage. With proper care, it can survive over 100 years or more. Still, you must keep the paper somewhere, and there is no better place than a safe. For this money, you can get a safe the size of a standard desktop drawer unit. It is more than enough to store all of your documents.
- Home And Vehicle Security Systems (4000$): Still using security systems without a network system can be pretty advantageous for you. An isolated security system can send you SMS messages when an event happens. Sure it is a little bit more expensive, but the only way of disabling such systems is by bringing a Faraday cage.
With a total budget of around 4700$, we achieved a pretty good level of security. Still, a determined attacker can penetrate this setup, but it will take him more time and resources. To break a safe, you should cut through it. And this generates sound. Sound is terrible for attackers, and it can alert neighbors.
In conclusion, just one more piece of advice. When you choose electronic devices (including a car) for your home, please research how smart the device is. The more intelligent it is, the more prone it is to hacking. Devices without Internet access are the best because the chance of hacking is relatively low or nearly zero.
Next part – here.