In the last couple of months, we discussed how you could achieve a good level of personal security for your team members. We covered the topics of physical information security, home network security, and finally, your hardware devices cybersecurity. With this article, we shall cover the issue of how you can upgrade your cybersecurity defenses as a team. The article will cover the necessities of remote-first groups because they are harder to defend. You can use the same approach to protect your office or shared space-based team. Still, the focus will be on underfunded small groups. At the end of the article, I shall present a sample budget for your team infrastructure.
But before going to the budget, let’s analyze how a remote team of workers communicates and collaborates. I shall list down the different infrastructure requirements for a technical IT team. Keeping in mind how digitilized our World is, they will work fine for any other distributed team.
Communication Channels
For every remote-first team, it is essential to have a communication channel. We can categorize the different communication channels by their speed. But let’s do this in the following list:
- Email: Email is usually categorized as an official communication channel, which we can use for communication inside and outside of your organization. It is heavily asynchronous, with messages response going from minutes to days. Usually, this kind of communication is used for strategic discussions and long-term plans. That’s the reason it could be the most valuable target for an attacker.
- Online Chat: Online chats are a faster way of exchanging messages. Usually, they are used when you need a quicker response from your peer, and there is no good time for a short, not planned call. Usually, the rule of thumb is to spend no more than 15 minutes chatting, and if the issue is not resolved, move to something faster. This one will be the second most significant target after the email for an attacker.
- Video Conferencing: This one is the fastest. Usually, it is used to exchange a burst of already prepared information. Most of the time, the data is a tactical one, and thus this way of communication is with the lowest priority for attackers.
Information Storage and Sharing
These days everything is done using information and files. But, you must store these files first and, after that, share them with your team members. Doing this using the standard communication channels is no good because there are no excellent categorization and tagging tools implemented in these systems. In short, they are not appropriately tailored for this kind of activity. That’s the reason the IT industry created a good amount of tools for solving this problem. Our small team will use them as well. So let me list them:
- Project/Product Management System: Project management software (PMS) can help plan, organize, manage resource tools and develop resource estimates. Depending on the sophistication of the software, it can manage estimation and planning, scheduling, cost control, and budget management, resource allocation, collaboration software, communication, decision-making, quality management, time management, and documentation or administration systems. As you can see, most of the vital information for your project/product will be in this system, making it an excellent target for an attacker.
- Cloud Storage Solution: Project management systems are outstanding in documentation storage, but they lack some of the features a full-scale cloud-based storage solution can offer. In this kind of solution, you usually store big files in a format such as video, audio, high definition graphics, etc. As such, you can leave a big part of your intellectual property lying in such cloud storage, making it a good target for an attacker.
- Automation System: Especially in IT teams, sometimes your team will need automated jobs to happen. If you have automation specialists, know how to write scripts, you can automate a big part of your daily routes. In the case of programming teams, this is usually building, deploying, and testing procedures for a new version of your product/project. It means that you have to give access from your automation system to your programming code, for example. And this makes it an excellent target for an attacker.
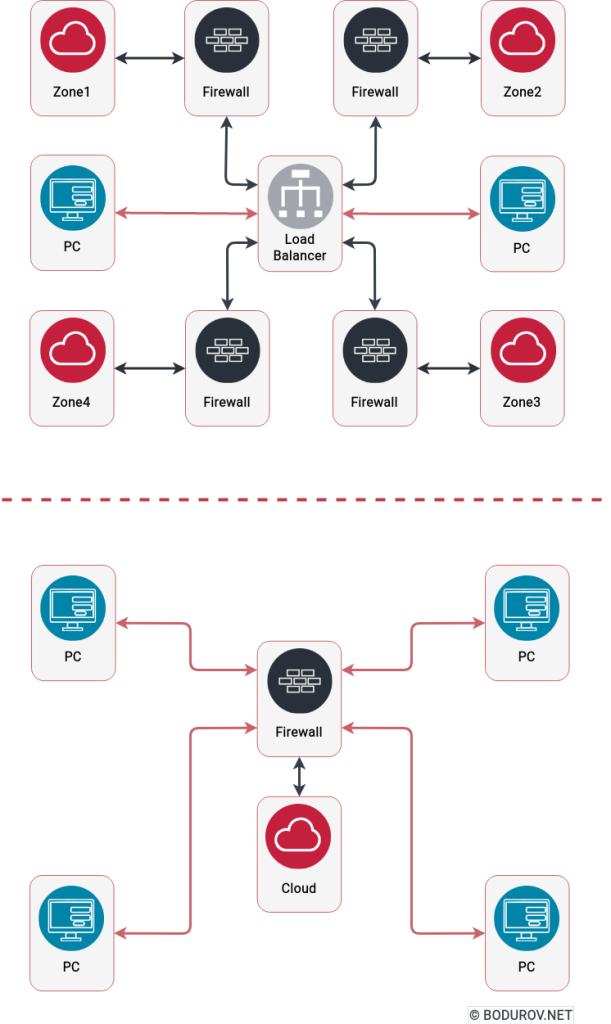
As we already discussed in the upper paragraphs, you need at least these six types of systems working and secured to have a functional remote-first team. Coming back to our knowledge of network defenses, the ideal solution for these systems is to be defended by VPN or a similar solution and expose only port 25 of the email server to support external communication.
Unfortunately, this kind of setup will be possible only if you deploy the services in your infrastructure. In the case of cloud providers, you don’t have much control of what is exposed to the Internet and how the cloud provider takes care of your security. Plus, the infrastructure is shared between multiple organizations, and there is no guarantee that these organizations follow such strict cybersecurity rules, such as your team.
Budget
But anyway, let’s create a budget for on-premise deployment of your infrastructure, and we shall use a VPS provider because it will be cheaper for us. A virtual private server runs its copy of an operating system (OS). Customers may have super user-level access to that active system instance, so they can install almost any software that runs on that OS. For many purposes, it is functionally equivalent to a dedicated physical server and, being software-defined, can much more easily be created and configured.
The most famous VPS providers are Amazon Web Services and Microsoft Azure. Still, there are some smaller players, such as Digital Ocean and Hetzner. As we shall do the infrastructure for a small team, we shall need a VPS with a not big pool of resources and go for the lowest price, which means CX1 instance in Hentzer. So let’s list now the different servers we shall need. All the prices are per month.
- Email And Chat Server(3.57$): As there will be no significant demand for these two services, we can place them on the same machine.
- VPN Server(3.57$): We shall have one machine for the VPN server, and all of the services without port 25 will be behind this VPN.
- GitLab Server(3.57$): Gitlab is a project management/automation system. As it can become quite a hungry beast, a standalone instance is a way to go.
- Video Conferencing Server(3.57$): One more hungry beast, it is a good idea to have it as a standalone server.
- Cloud Storage(9.31$): This one will be a CX1 instance + an additional 100GB to store larger files. For a small team, a total of 120GB will be enough.
With a total budget of around 23.59$ per month, we achieved a pretty good level of security. Still, a determined attacker can penetrate this setup, but it will take him more time and resources. We shall use the standard VPS provider firewall. Still, if we want to achieve a higher level of security, we could add a server that will serve as a software-based firewall and IPS solution. Additionally, there are Open Source solutions for all the services types, and they will cost us 0$ per month.