As you can see from the previous paragraphs, there are multiple ways to penetrate your devices. In the following sections, I shall list some methods of making your devices more secure. You can find the previous part – here.
Hardware Security
There are multiple options for physically securing your laptop and smartphone. At the end of the article, I shall give multiple variants for your budget, but ideally, the essential hardware security upgrades are:
- Secured Notebook Backpack: There are multiple hardware vendors for securing your laptop backpack. It is essential to know the standard branded bags do not offer enough security options. For example, most backpacks do not provide RFID protection and proper locking mechanism.
- USB Port Lockers: Port lockers can keep your laptop safe from Rubber Ducky-based attacks. At the same time, port lockers are pretty interesting because they make attackers’ lives more complicated in case of steal. To access the USB port of the device, they have to break the locker, which can damage the USB port and make it unusable.
- Hardware Tokens: Bussines series laptops usually come with internal TPM chips, which can encrypt your entire hard drive. It is terrific, but if you want better security, it is advisable to encrypt your most critical files using external USB hardware tokens.
Antivirus Software
The average number of new malware programs per day is around 450 000. It is an astonishing number and almost destroys the necessity of antivirus software. Still, it is crucial to understand that the goal of your Antivirus Software is to stop the most critical pieces of malware, but not all of them. Let me list some of the mechanisms your Antivirus Software uses to keep you safe.
- Malware Database: Every Antivirus program comes with a malware database with different strains of already analyzed computer malware. As we already understood, there are around 450 000 new strains per day. Antivirus companies’ teams keep only the most dangerous strains in the database to keep with the speed of making new strains.
- Malware Scanner: Usually, every malware tries to gain access to resources, which are not part of its resources pool. Antivirus software can monitor your operating system for such activities and can block them and finally notify you.
- Operating System Files Hash Check: Some antivirus software can check whether there are changes in your operating systems and notify you and revert the system files for the previous state. It is especially true with Red Hat-based Linux distros.
Open Source
One of the reasons people choose Open Source is the level of security it offers. You can perfectly set up your business to use an open-source stack from the beginning. And this is not only the applications but the operating system and even your hardware. Especially Linux is a beautiful example of how an Open Source ecosystem can increase its security by being open. Instead of using pirated software, you download it from a free repo, which has the source code of the app already reviewed. Every major Linux distro has all of its packages signed, and the repo can verify them. But let me list the different advantages an open-source operating system has.
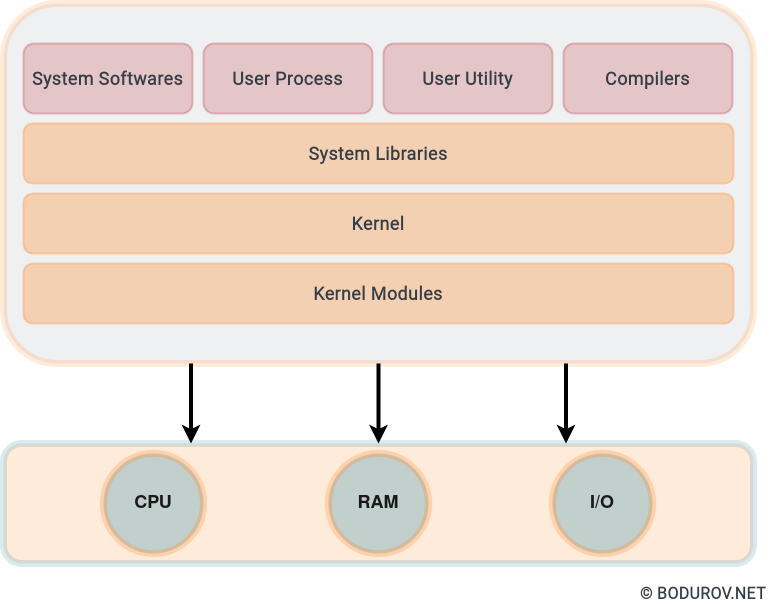
On the diagram, you can see a sample architecture of a Linux system. Usually, SELinux and AppArmor are working on the Kernel level. After version 4.4, Android has SELinux enabled by default.
- SELinux and AppArmor: SELinux and AppArmor are kernel modifications and user-space tools added to various Linux distributions. Its architecture strives to separate enforcement of security decisions from the security policy and streamlines the amount of software involved with security policy enforcement. Significantly, the fundamental concepts underlying SELinux can be traced to several earlier projects by the United States National Security Agency (NSA).
- Open Source Repos: All the packages are part of the software repos, maintained by the distro authors. Bigger Linux distros such as Red Hat and SUSE support big security teams to find and patch holes.
- Open Source Hardware: There are multiple open-source hardware initiatives, including PowerPC and ARM-based processors. It is essential to know those hardware devices attached to your PC come with drivers, and sometimes these drivers can be an entire operating system. For example, server-based Intel Xeon processors come with network-based remote access control.
Budget:
So after we have listed most of the penetration vectors which an attacker can take, we can finish the topic by creating a budget. We will focus the funding towards underfunded organizations with a limited budget for their cybersecurity program. The budget will be per employee.
- Pacsafe Backpack (190$): Pacsafe is a brand of travel equipment emphasizing anti-theft features. The company’s products include adventure backpacks, urban and leisure bags, women’s bags, photography bags, luggage, and travel accessories such as straps, cables, and locks. Their middle-end backpacks offer a pretty good level of security.
- Business Series Laptop (1000$): For this one, I would choose Lenovo Thinkpad-based laptop. It supports TPM and will offer a good level of harddrive encryption. It is essential to mention here that you have to encrypt all of your storage drives, no matter SSD or HDD ones.
- Laptop Operating System(0$): Here, we shall go with either CentOS or OpenSUSE. I would personally go with CentOS here because of the native SELinux support. If you want to use the Ubuntu operating system, you should live with AppArmor or set yourself SELinux. CentOS additionally support free Antivirus Sofware supporting all the listed features in the previous paragraphs.
- Smartphone(200$): Here, we shall use any device, which supports LineageOS. LineageOS is an operating system for smartphones, tablet computers, and set-top boxes, based on Android with primarily free and open-source software. It is the successor to the custom ROM CyanogenMod, from which the devs forked it in December 2016. It offers a good level of privacy, including the complete removal of the Google Play Store for the most paranoid ones. Most of the devices officially supported are in the 200$ range.
With a total budget of around 1390$, we achieved a pretty good level of security. Still, a determined attacker can penetrate this setup, but it will take him more time and resources. If you want to improve this setup further, you can add USB locks and hardware tokens. But, again, the improvement will not be much because, in case of hardware steal, hackers would have to break your TPM module, and the TPM modules are designed to resist this kind of attack.
To be continued