Once the top interest of the state was its national integrity and the protection of its borders, that no more seem like the top priority with the rise of globalization. The world has now turned into a global village, and everyone is interconnected. We no longer base the international policy on the principle of expansionism but more on soft and indirect interventions. Cyber-attacks have become very common these days to steal sensitive data or block a critical infrastructure of any country by targeting its vital computer systems. State governments sponsor part of these cyber-attacks to penetrate rival states. Criminals execute another piece for the sake of financial gains.
State-Sponsored Cyber Soldiers:
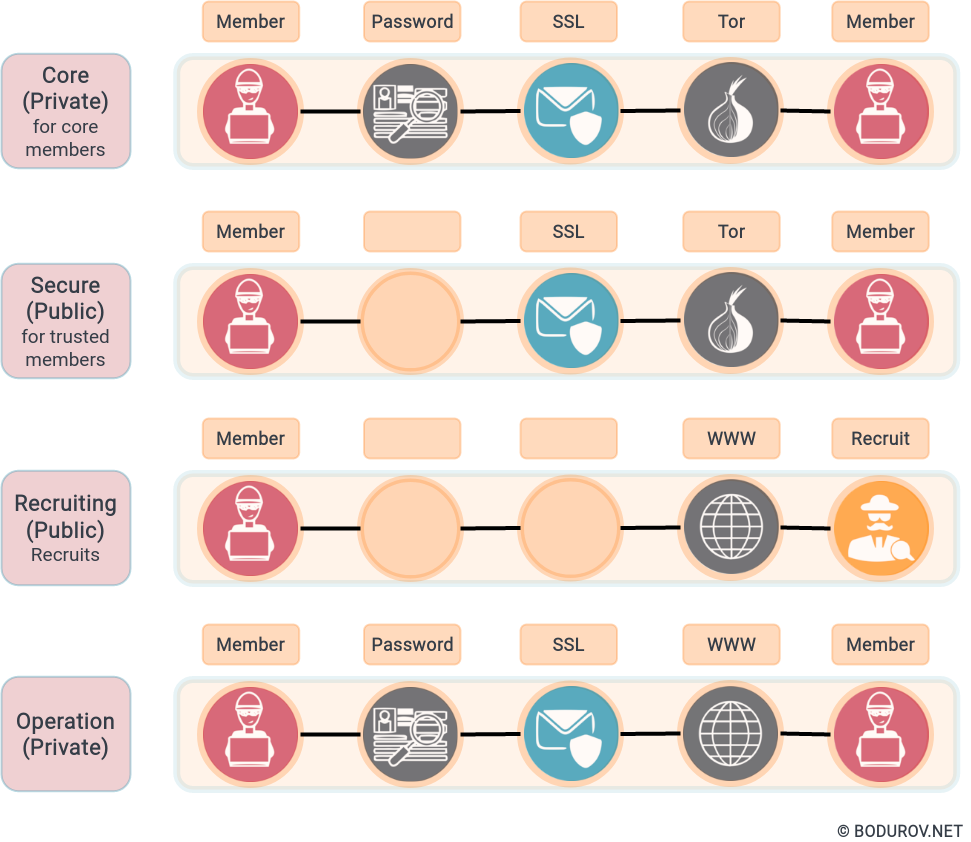
Despite having conventional solid militaries, many countries are putting efforts into arranging training programs for cyber soldiers who are getting themselves ready for cyber warfare. They are picking up the best people from network exploitation, malware, or firmware reverse engineering. It is essential to understand that cyber warfare usually has asymmetric nature. A small unit attacks a relatively bigger target in terms of resources. That’s the reason these people receive additional training in guerilla warfare by top military specialists.
Everyone is welcome to the party:
Almost every country now has a position regarding cybersecurity. And every country confirms that it has or wants to have highly developed cyber warfare systems. Although most countries are strictly against the use of military cyber systems to access the sensitive data of any other country, they keep on developing their cybersecurity platforms. An analysis of cyber capabilities of one relatively big country from 2009 to 2015 showed seven major cyberattacks origin from it. The hacker group tried to hack everything, starting from simple data theft from technological companies to hacking a Personnel Management office of a government agency.
Unofficial cyber attacks:
Not all cyber attacks are for getting to know the secrets of other nations. Sometimes cyber attacks are used to gain access to critical infrastructure and gain leverage during war actions. Cybersecurity is vital during these wartime operations, keeping in mind that now almost everything is digital and modern armies use more and more information systems to increase their efficiency on the battlefield.
There are several other examples where unaffiliated groups were involved in violating cyberspace. Most cases even show that the state government is well aware of these groups but does not act against them. These attacks bring betterment for the state, so as long as they benefit the government, it does not interfere in their matters but even shields the hacker groups. If they use their skills to steal money, the money comes to the home state, which is beneficial for state economics. That is why governments often allow such hackings in their territory.
Many unofficial and unethical cybercriminals are the silent pupils of state-sponsored cyber actors. They learn the tricks from the big boys but use them for other malicious reasons and financial gains. It is essential to understand that these days everyone is a target. Especially having in mind that many states manufacture and use military-grade malware. Later this malware can be recycled by criminals and used versus non-state level organizations or even small and medium businesses.